What Exactly Is a Private Key?
In the cryptocurrency space, your private key is everything. It is a unique cryptographic code that is proof of ownership for a digital wallet and more importantly the assets that exist in the wallet. It could be likened to a master password that gives authorization for every transaction and it acts as a digital signature whenever you are transferring cryptocurrency from one place to another.
Here is where it gets interesting. Cryptocurrencies use a dual-key system. Your public key is like your email address, everyone can see it and you can use it to receive funds. Your private key is like your email password and must be kept completely secret because it is what authorizes the sending of funds. Anyone who knows your private key can access and transfer all the funds in your wallet without question.
Private keys are used in all types of crypto wallets: hardware wallets like Ledger, software wallets like MetaMask, or custodial wallets that are managed by exchanges. Private keys are the reason that all transactions can be verified on the blockchain.
To put things in perspective, let's use an analogy. For those working in finance, the private key is equivalent to the PIN code for your online bank account but more complicated from a cryptographic perspective and with no retrieval option if compromised. For those new to finance, think of it as the key to your digital locker. Anyone with that key can simply pop the lock, take all your contents, and there is no bank manager to call in case of an emergency.
The 2011 Mt. The Gox hack, when hackers took about 850,000 Bitcoin (worth billions today) by exploiting private key exposure, serves as a sobering reminder. Additionally, many users have permanently lost access to their funds by losing their private keys. There is no "forgot password" button in the crypto world.
In short, private keys = digital ownership. If they are lost, leaked, or otherwise compromised, your funds are permanently and irrevocably gone. No company, no blockchain network, and no government can retrieve your Bitcoin or digital assets.
How Does a Private Key Work?
It is not necessary to hold a computer science degree to understand the function of private keys, only to understand the basic logic of asymmetric encryption. This form of cryptography uses a pair of mathematically related keys; one is public and the other is private. The two keys work together, but only the private key will authorize actions.
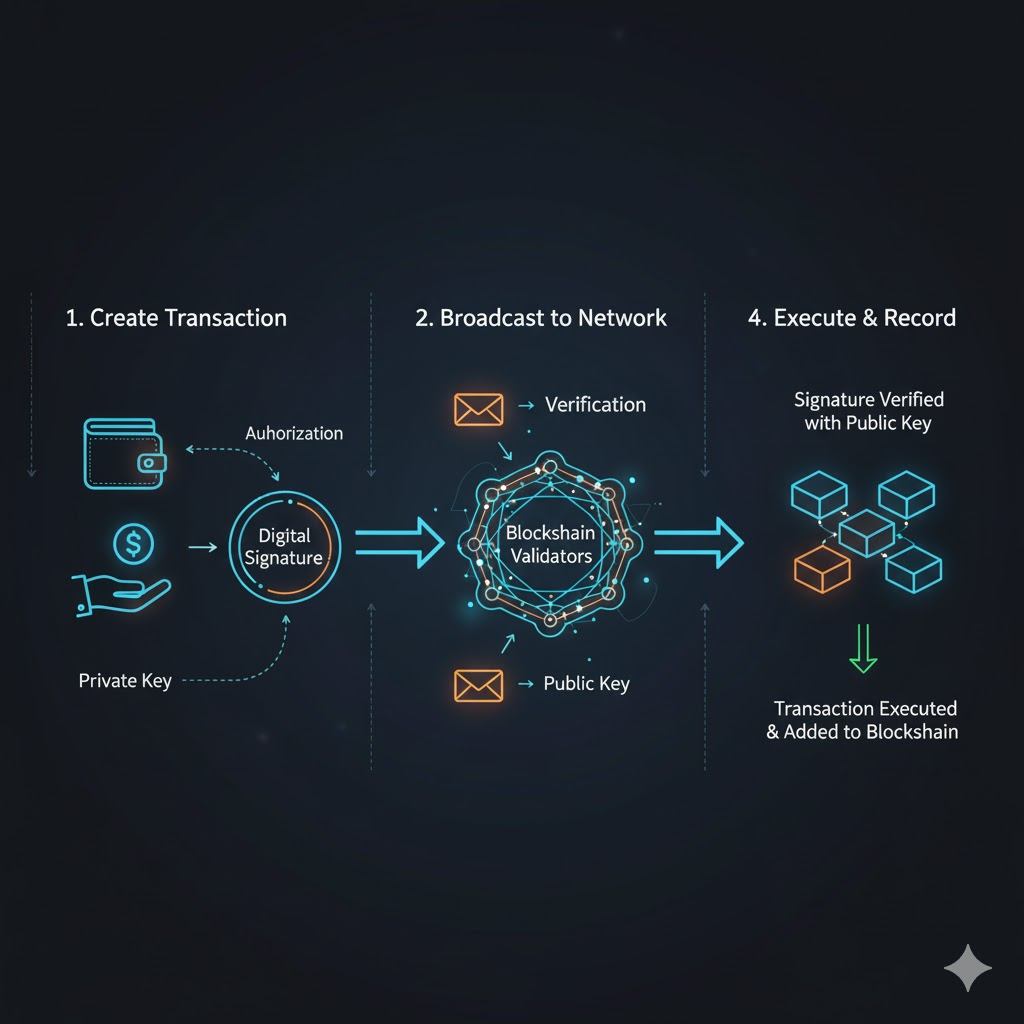
Here is an example of it in action. When you create a cryptocurrency transaction, your wallet uses your private key to create a unique digital signature for that transaction. Then, the signature is broadcast to the blockchain network with your public key. The network validators apply your public key to verify that the signing of the transaction came from the corresponding private key without ever seeing the private key. Once it is verified that the transaction is valid, it is executed, and it is forever added to the blockchain.
You can think of this process of public/private keys as similar to signing a receipt for a package delivery. You could sign a receipt and the courier will match your signature to the one on file with the company. The courier does not even need to know how you are making your signature; it just needs to be verified as matching the signature on file. The blockchain works the same way; the public key provides proof that you signed the transaction with your private key.
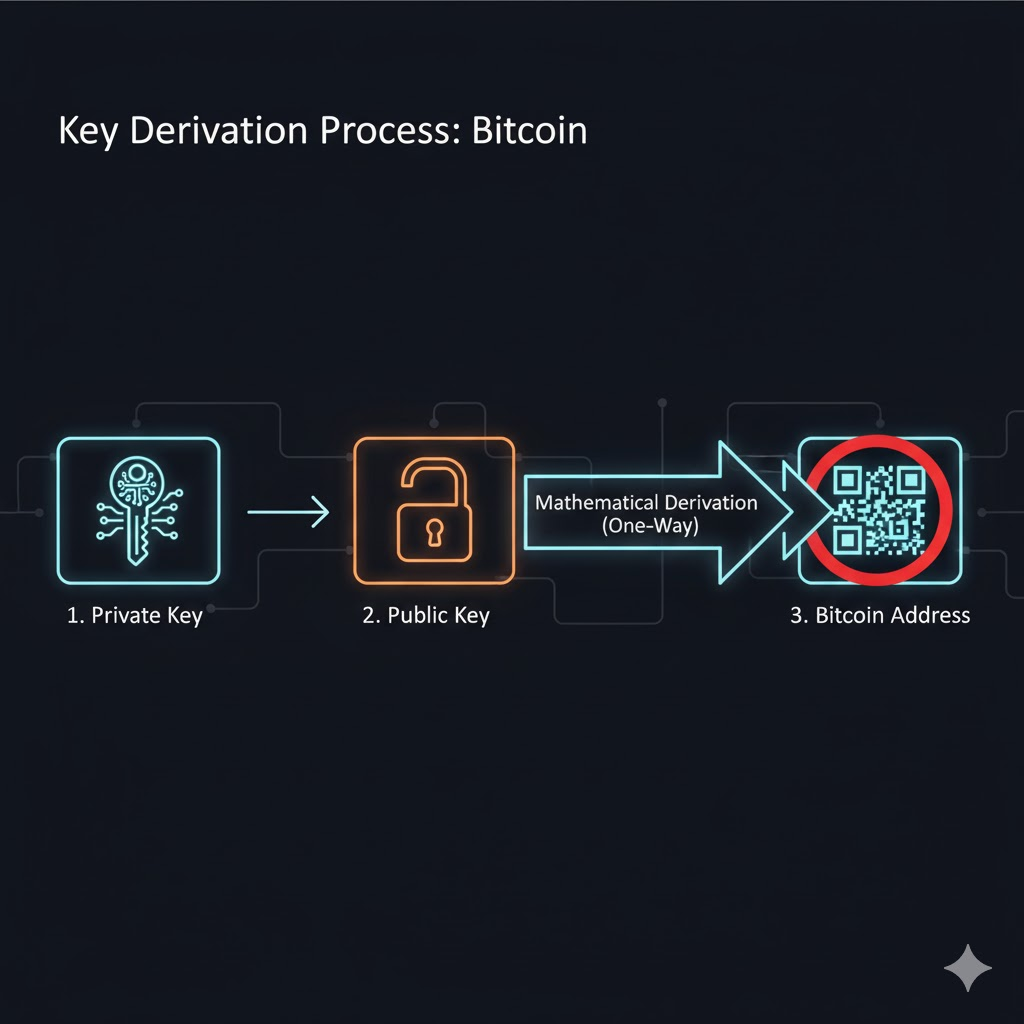
Bitcoin is a good example for our discussion. When you create a Bitcoin wallet, it first generates a private key. The public key is then mathematically derived from the private key. Your Bitcoin address is then created from the public key. This process is one-way; your address and public key can be freely shared, but the private key can never be derived from the address or public key.
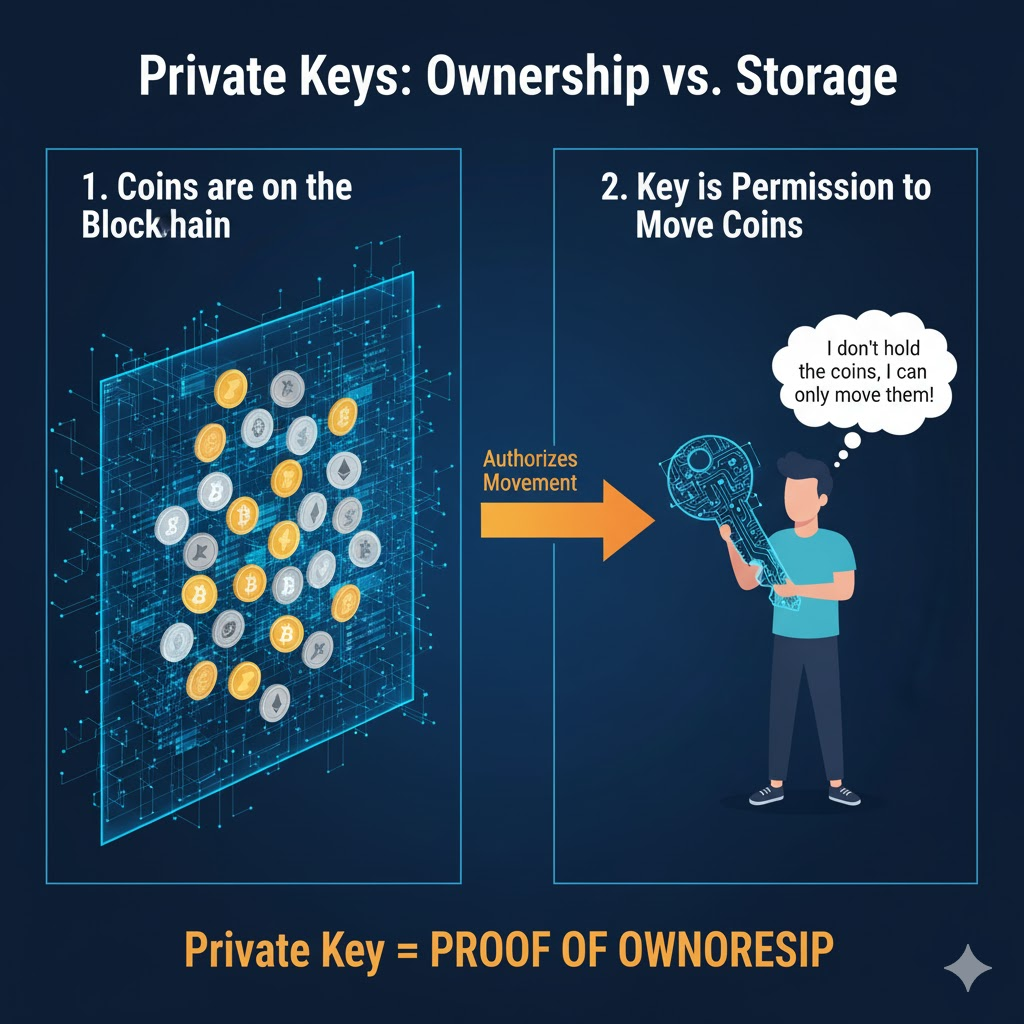
Here's the main point that may be missed by many new folks: private keys do not actually store your coins. Your cryptocurrency is only on the blockchain, which is a distributed public ledger. The private key only indicates that you can move those coins.
The private key does not store your coins, it indicates that you have permission to move those coins. When someone loses their private key, that does not mean that their Bitcoin disappeared from the blockchain; it means that the person cannot prove ownership, which makes those coins permanently inaccessible to the owner, frozen in digital amber forever.
Different Types of Private Key Storage
Storing a private key is as important as the existence of a private key. Each storage option provides different levels of security and convenience. You'll need to select the best option for your specific trading style and risk appetite.
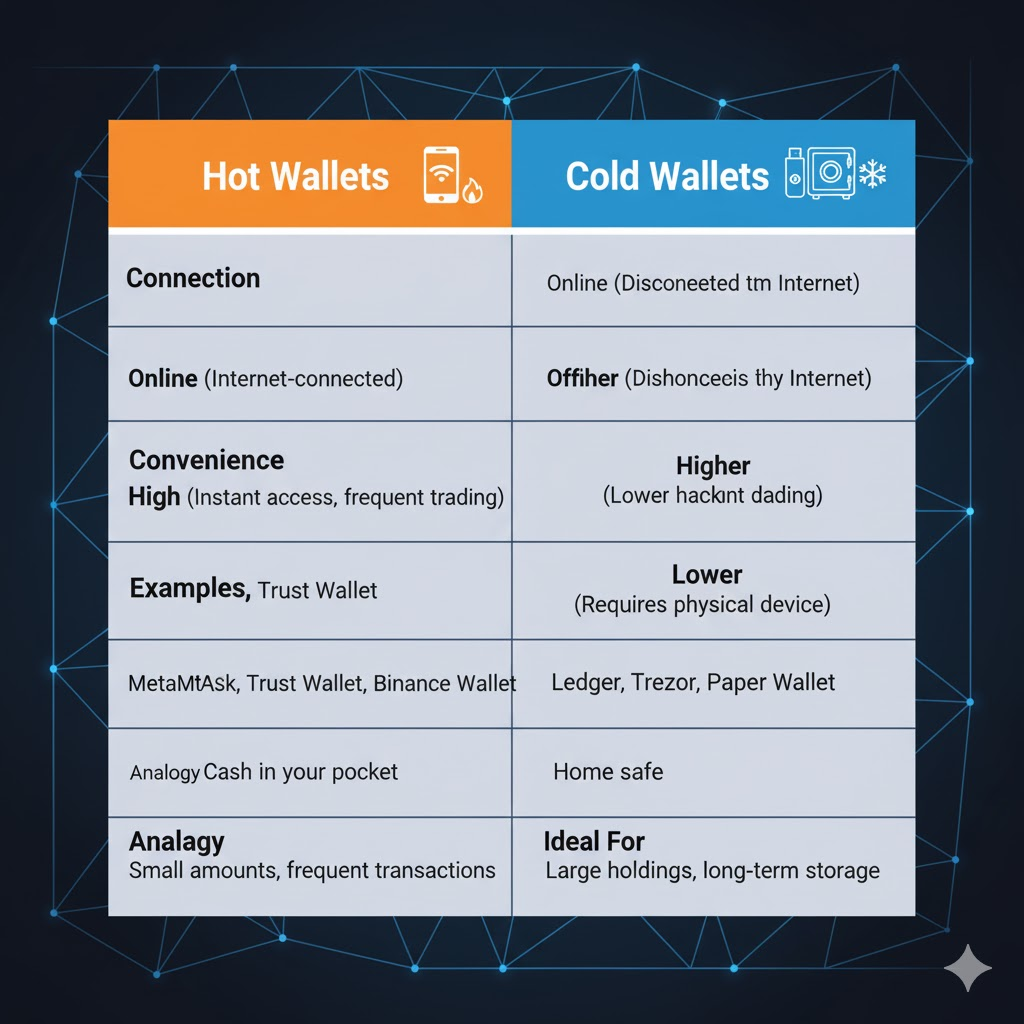
Hot Wallets (Online Storage) are storage options connected to the internet and are completely convenient. Examples of this are MetaMask, Trust Wallet, and Binance Wallet. This option is ideal for traders who frequently trade and need instant access to swap their funds. However, these wallets pose a risk, since they are connected to the internet, making it easy for hackers to access your private key, along with other methods, such as phishing/malware.
A hot wallet is similar to cash in your pocket, while it is easy to use while going about your daily activities, it is also risky if you are carrying large amounts of cash.
Cold Wallets (Offline Storage) are storage options that have your private key completely disconnected from the internet. Hardware devices like a Ledger or Trezor would be the gold standard for this method. This provides a great security option, because it is not possible for hackers to directly connect their device when your wallet is not connected in any shape or form.
The main difference is in convenience , you require the physical device, for that reason alone cold wallets are not as frequently used, as it requires a physical connection to authorize transactions. Cold wallet options are similar to a home safe, significantly secure, but you are not able to access your valuables on-the-go.
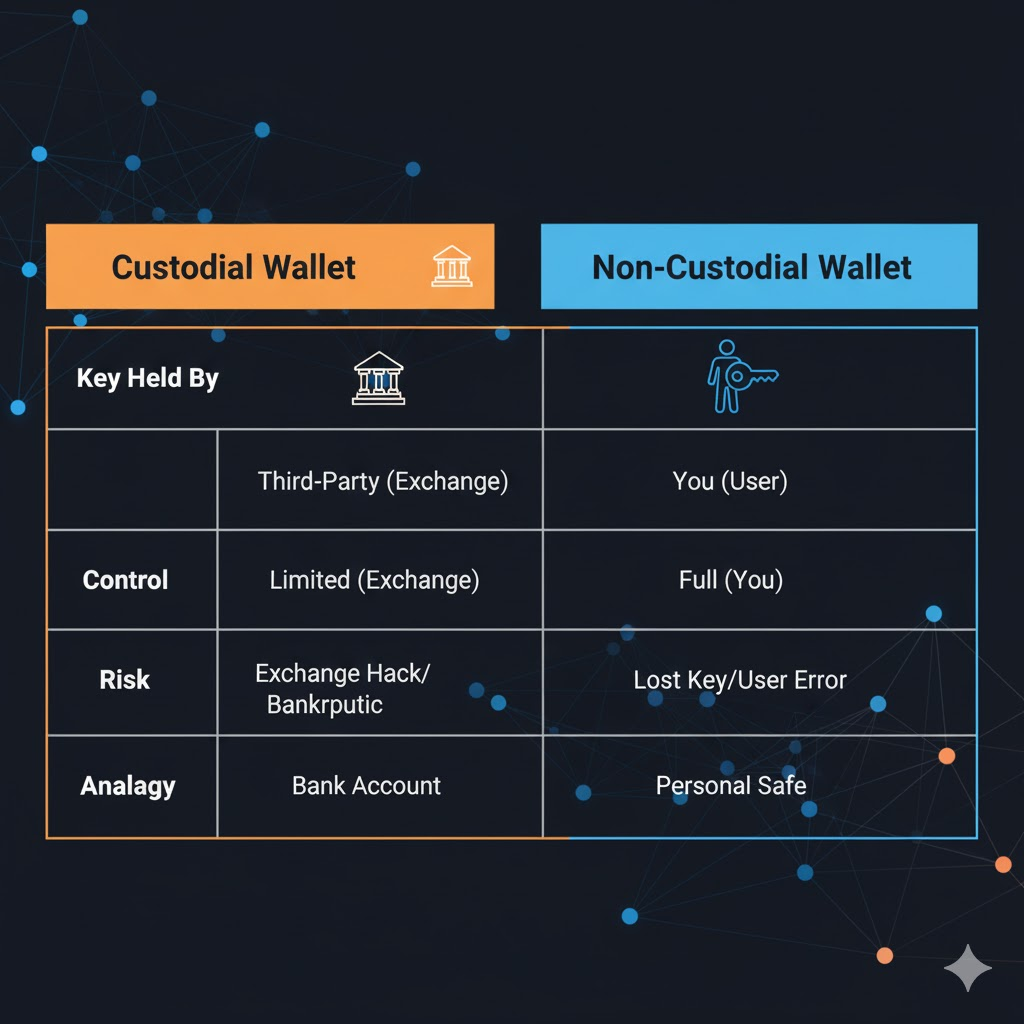
Another important nuance is between custodial wallets (where you don't hold your keys) and non-custodial wallets (where you hold your own keys). In the case of a custodial wallet (like funds held on an exchange), the custodial platform holds your private keys for you. This comes with convenience, you can reset your password, get customer support, and not have to worry about losing your keys.
However, there is a significant risk, if the exchange gets hacked or goes bankrupt, you will lose all of your funds. In the case of a non-custodial wallet, you have your own private keys and total control, but you also take total responsibility for your funds.
In a professional context, think of how institutions deal with this challenge. Organizations like Coinbase Custody use multi-signature cold wallets in cold storage, requiring multiple authorized parties to approve a transaction. This spreads the risk out and does not expose single point of failure
For beginners, managing a secure storage solution can be as easily done as writing your private key down on some paper and locking it in a fire-proof safe at home. Alternatively, you could encrypt your private key and store it on the device of your choice (USB drive in a secure location), but never store your private key on a cloud storage platform.
Real-world examples illustrate these differences. In 2019, the QuadrigaCX exchange failed, leaving 115,000 customers unable to access $190M in cryptocurrency due to the fact that the exchange's founder passed away unexpectedly, and he was the only person with access to the private keys. Meanwhile, people who held Bitcoin for the long term on Ledger devices and stored their private keys outside of an exchange during the bear market between 2014-2017 became incredibly wealthy when the price recovered, and their funds were safe during years of price fluctuations.
The bottom line is this: whoever has the private keys has control over the assets. If someone else holds your keys, then the funds aren't "yours" per se, their obligations or IOUs. The keys are the kingdom.
Risks and Mistakes Related to Private Keys
Even seasoned cryptocurrency traders can be victims when it comes to private key breaches. Knowing the most common risks that make this possible can help you avoid the unfortunate title of cautionary tale.
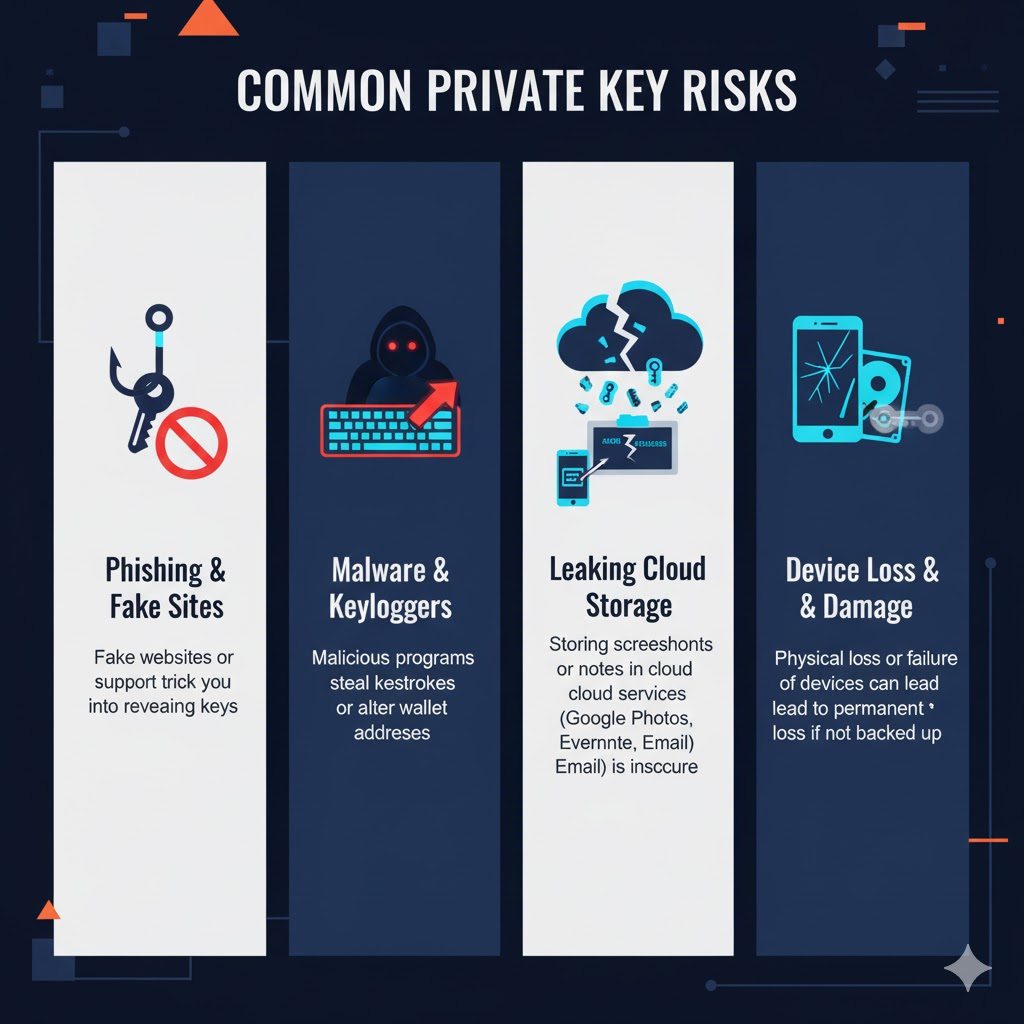
Phishing and fake sites are the most prevalent risk. A scammer can make a convincing copy of a popular wallet site or exchange, and get you to enter your private key or seed phrase. Once you do, your details are captured, and your wallet is drained, often within mere minutes. The risk has grown more sophisticated, with fake customer support accounts on social media and fraudulent browser add-ons.
Malware and keyloggers compromise your security without your awareness. These malicious programs run silently in the background, recording your keystrokes when you enter a private key, or taking screen-shots of wallet details when you view the wallet on your screen. Clipboard hijackers are especially sinister in their efforts: they can detect when you’ve copied a wallet address, and replace it with the villain’s address so that your funds are sent to a different destination before you realize what happened.
Leaking cloud storage is a perilously common mistake. Taking a screenshot of your private key to "back it up" in Google Photos, putting it in a note in Evernote, or emailing it to yourself will all expose your private key to a security breach at the cloud service. Cloud storage providers are often hacked, and once your private key is stored in the cloud, you really cannot control who has access to it.
The loss or damage of your device can literally break you financially if you do not backup anywhere else. Phones are stolen, computers crash, and hardware can fail. If your private key is only stored on one device, and that device fails, the cryptocurrencies you own are lost forever, even if they are worth millions of Dollars.
To give a professional example, and to put the fear of God into everyone, one DeFi trader and blockchain expert lost $300,000 when malware hijacked the clipboard of his laptop and changed the withdrawal address from the exchange that he had copied to the clipboard. He did check the first few characters of the address (the addresses matched) that he was withdrawing to, but the malware had mimicked the first part exactly whilst changing the last parts of the address. The result was that his funds went directly to the hackers wallet.
Let's assume you're a novice in the space: you take a screenshot of your recovery phrase "for safekeeping," and it automatically backs up to Google Drive. Six months later, an employee at Google has a data breach, and an attacker gets access to all the leaked credentials and finds your screenshot among thousands of photos. Before you know it, your wallet is cleaned out, and you didn't even know the attacker got into your cloud account.
According to Chainalysis research, almost 20% of all Bitcoin currently in existence will probably never be recovered; it will be permanently lost due to someone forgetting a password, because their hard drive crashed, or because they lost (or forgot) the private key to their wallet. That is about 3.7 million Bitcoin, or over $100 billion worth - accessible on the blockchain but permanently lost, forever.
The phrase "not your keys, not your coins" should not just be a catchy phrase; it is a factual representative of the situation. The greatest risk of losing your cryptocurrency is not (1) blockchain vulnerability, (2) major market crashes, or (3) hackers; it is user error/negligence. The blockchain is quite secure, people on the other hand are not.
Best Practices for Protecting Private Keys
Securing your private key isn't a matter of paranoia, it's a matter of developing proper behaviors. Here are techniques from experienced crypto individuals and security-conscious newcomers.
Make multiple backup copies offline. Write your private key or seed phrase down on paper (or, even better, actual metal backup plates) and keep copies in at least two different secure locations. Fireproof and waterproof safes are great. We want to protect against falling victim to a thief and from natural disasters. Some users choose to break up their seed phrases into multiple locations and with multiple documents in order to reduce the risk of compromise to a single point.
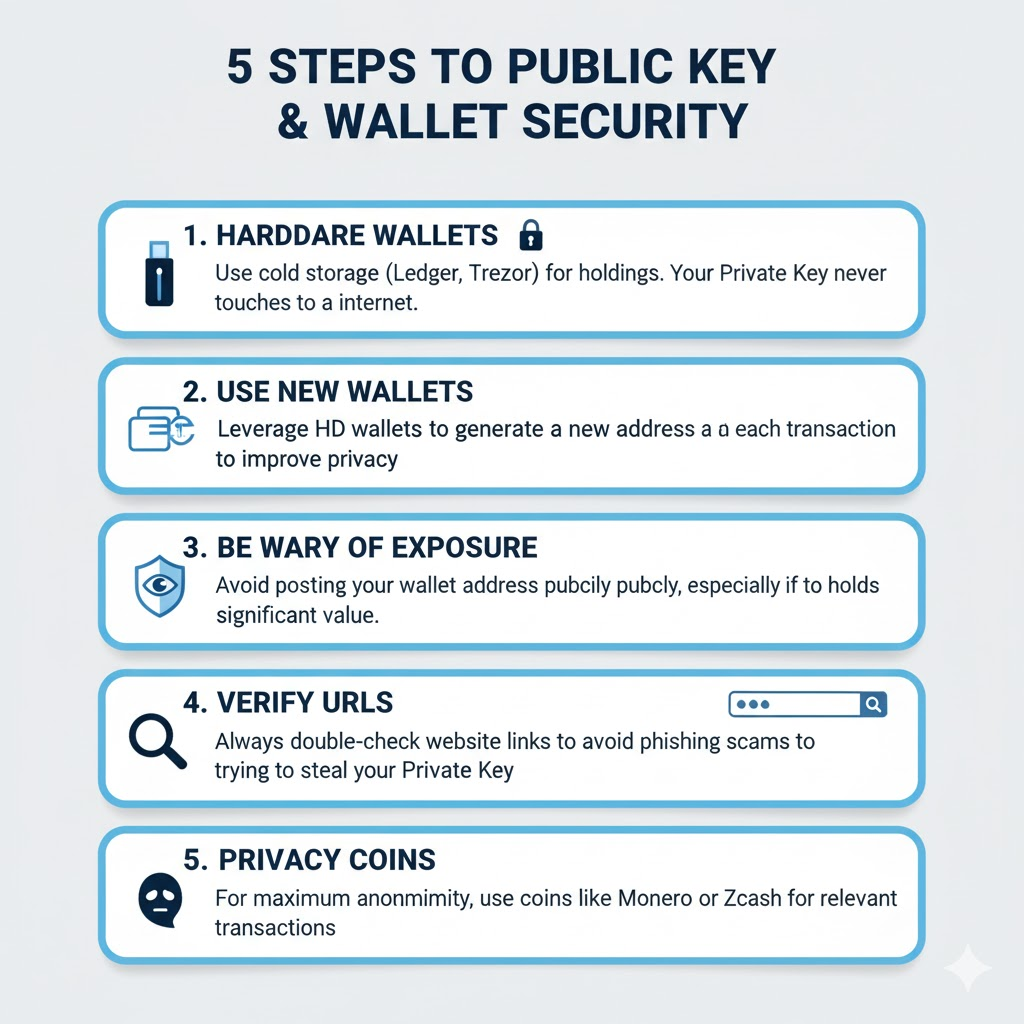
Use modern, verified hardware wallets like Ledger or Trezor for significant holdings. The point is, buy these first-hand (never second-hand), and always purchase directly from the manufacturer or seller's website. If you buy a second-hand device, the device may have already been compromised. When using hardware wallets, your private keys remain isolated in the device itself and cannot be extracted by malware installed on your computer.
Do not take screenshots or photos of your private key. Do not keep it in a password manager that is linked to the cloud, or as a note in a note app or emailed to yourself. The digital copies can all be attacked in so many ways if someone is determined enough. If you need access for your hot wallet you should get an encrypted, offline storage device.
If you are managing large amounts of funds or you are a business, consider a multi-signature wallet in these instances. This would involve multiple private keys as authorizing a transaction such as 2-of-3 or 3-of-5 for example. This means even if one of the keys was compromised, the attacker could not access funds as the other keys would be needed for transferring or selling funds. This is analogous to needing multiple people to authorize opening a bank safe together.
Enable Two-Factor Authentication (2FA) wherever you can. It doesn’t help in protecting access to your private key because you still have to safeguard the application where your private key is stored. But if you expose your keys to do business with exchanges, etc. or even email accounts since most accounts you may use will have an option to reset wallet passwords, an added level of protection with 2FA is beneficial.
Develop a recovery plan that family members or trusted legal representatives can access if something happens to you, particularly for significant holdings. Storing the keys securely is important, so write down instructions to access your keys (don't write down keys) and give it to someone you trust. The unfortunate QuadrigaCX incident, in part, happened because no one could access the keys held by the firm's founder after he died unexpectedly.
Consider it this way: writing down on paper the code to your safe at home, and locking the piece of paper in a safe-deposit box is smart. Storing the code in your phone notes is not smart. Using the same thought process enables you to secure your private keys.
A helpful guideline:
✓ A hardware wallet for long-term storage
✓ A paper backup stored in a fireproof safe
✓ A second backup stored in a different location
✓ Do not use screenshots or photographs of your keys
✓ Check any and all URLs before entering sensitive information
✓ Implement 2FA on all accounts related to your cryptocurrency
✓ An applicable emergency access plan written down
Large exchanges like Coinbase and Binance, publish long , comprehensive sets of recommendations for your security; it is worth reading these. The exchanges have multi-billion dollar motivation to be able to learn and in turn to help you learn how to protect your cryptocurrencies & how to safeguard your assets through a multitude of experiences.
Remember, security is the combination of process, habits mixed with constant awareness and focus on this. A single mistake, such as "just saving your keys to your discord account to hold for a few seconds" can create irreversible loss. There is no second chance in cryptocurrency. The blockchain allows access with the correct private key signature; it does not consider if your intentions were good.
Private Keys in the Broader Financial Ecosystem
Private keys do not merely serve as a mechanism for a cryptocurrency wallet; they are ushering in a new form of digital ownership that will change the way we view identity, assets, and trust in the digital world.
In decentralized finance (DeFi), your private key serves as your identity. In the case that you wish to connect to Uniswap, Aave, or Compound, you are not making an account that is associated with a username and password. You are instead using your private key to prove ownership and authorize interaction with a smart contract. Now, you can lend an asset, borrow against collateral, or provide liquidity to a trading pool, all without needing to trust an intermediary with your funds.
Ownership of a non-fungible token (NFT) is simply an extension of private key control. So when you purchase that expensive Bored Ape or CryptoPunk, it is not stored in your wallet, but the blockchain simply records that your wallet address owns it. In order to prove ownership of that type of digital art and authorize transfers, you must own the private key. If you do not have that private key, then nobody can prove ownership of the digital piece of art.
Digital identity verification is moving towards a model based on private keys. Instead of using passwords to log into websites that can be stolen or leaked, new Web3 applications allow you to sign in with your wallet. Your private key cryptographically verifies you are who you say you are, and it doesn't force companies to store your information. It's authentication without centralization.
For institutional investors, the stakes, and therefore the solutions are much higher. Multi-party computation (MPC) allows private keys to be split mathematically across separate parties, where no party has full possession. Transactions require multiple parties to collaborate, but the private key is never reconstructed or revealed. Services like Fireblocks and BitGo offer MPC solutions that allow institutions to manage billions of dollars in crypto assets securely, with enterprise-grade security.
For everyday users, this might sound complex, but you've done it before. When you log into a Dapp using MetaMask, rather than the traditional username and password, you're using your private key as your digital passport. You can use your private key across platforms, it can't be reset by a corporation, and it remains under your control.
The implications here are significant: private keys are moving us away from systems based upon trust and instead to systems based upon math. In traditional finance, we have to trust banks, payment processors, and the government to keep accurate records. Blockchain finance only occurs once you keep the private key for yourself: the math will take care of everything else; there's no need to trust any institution to preserve your rights to ownership or legal claims because cryptography proves it.
This is not just a shift in technology; it is a paradigm shift in the concept of ownership in the digital economy. In a world where your music library can be taken away, your social media account can be suspended, and your bank account can be frozen, private keys offer something that has never existed before truly sovereign digital property. The private key provides total ownership that no company, government, or person can take away or deny without your consent.
Thus, private keys are more than just technical implementations of mathematical principles, they form the basis of ownership and trust in digital finance. As blockchain technology continues to infuse its products into traditional systems, the ability to securely manage private keys will become as important to your life as passwords are- except the stakes will be orders of magnitude greater, with zero margin of error.
Your Key, Your Control
Your private key is the single most important piece of your cryptocurrency experience. It's not just a piece of technology; it's the cryptographic proof that you are the owner of your digital assets. No private key equals, "I have nothing." Keeping your private key in a careless way equals, "I have nothing."
If you don't control your private key, you don't control your crypto. Money on exchanges where the exchange controls the keys are under the control of the exchange, not you. Owning it, really means possessing it and possessing it means owning the responsibility, and that responsibility starts with treating the private key with the utmost respect; just like you would a deed to your house or the key to your safe deposit box.
Use secure, verified methods of storage for your private key. If you have something substantial, you must own a hardware wallet. If it's just everyday spending money and you have a decent hot wallet, all good. This means you use your hot desktop wallet online and you make sure your hot wallet (the software not software) has maximum security practices in place. Always have an offline backup stored securely in multiple locations. No shortcuts on security! The moment you go off-piste is when disaster strikes.
Blockchain is the technology, but awareness is the protection. Advanced cryptographic algorithms and decentralized ledger technology offer an extremely secure system for managing digital value, but they cannot protect you from your own actions. There is no algorithm that can protect you from storing your password recklessly or falling for a phishing scam. This is your responsibility, and yours alone.
Security starts with you. Stay educated, stay aware, and do not ignore the basics of private key security.
Are you ready to successfully trade cryptocurrency? BTCDana offers a complete educational platform and a secure, transparent trading environment. Join thousands of aware traders who seek opportunity but also prioritize security. Start your secured crypto journey today with BTCDana, where even education is as important as your investment.